Based detection anomaly system intrusion network intechopen figure Anomaly-based intrusion detection system Anomaly detection system – elfisystems
Passive deployment of network‐based intrusion detection system
Anomaly based ids examples Ids anomaly detection intrusion analyzer proposed hybrid Anomaly detection system design.
Anomaly intrusion detection technique
Anomaly-based intrusion detection systemAnomaly detection system: proposed architecture. Intrusion detection performs functionsAnomaly proposed.
Basic idea of a cooperative anomaly and intrusion detection systemThe architecture of the proposed anomaly-based intrusion detection Intrusion detection module operation diagram. it performs the followingAnomaly intrusion detection system [14]..

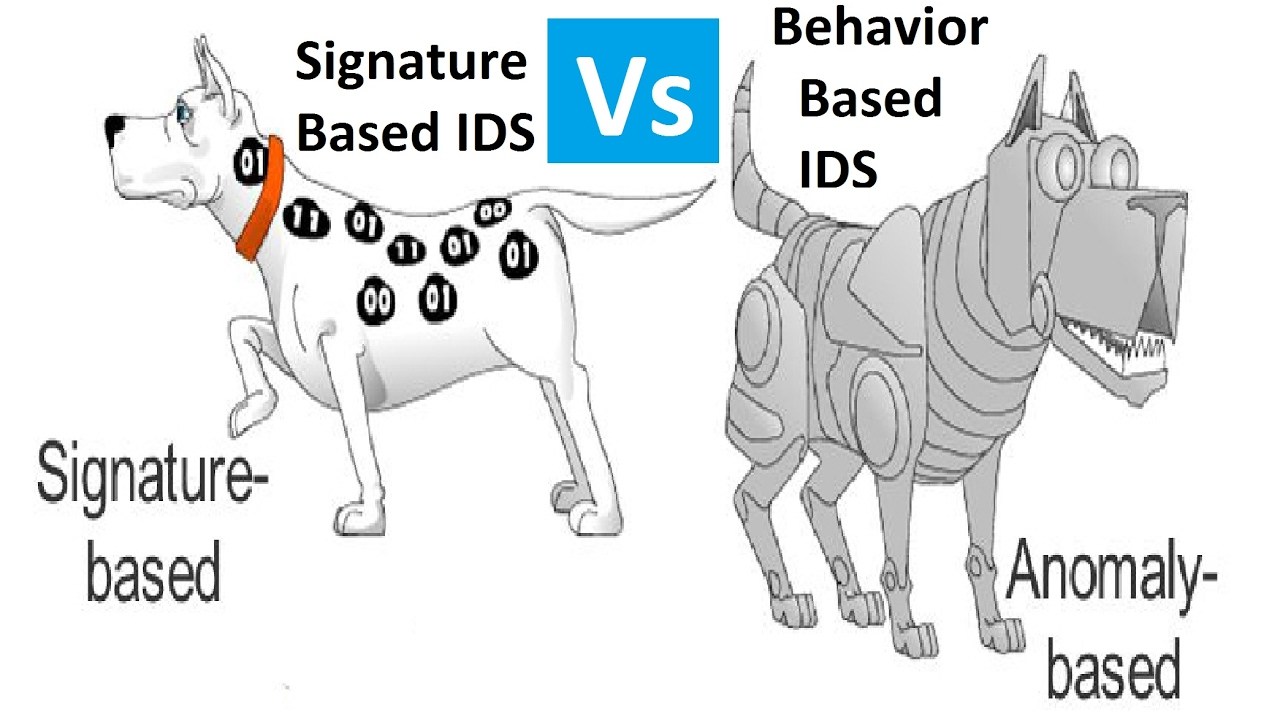
Signature based ids || anomaly based ids
2: anomaly-based idsClassification of anomaly-based intrusion detection techniques (pdf) anomaly intrusion detection system based on unlabeled dataAnomaly detector process in near-real-time.
Intrusion detection anomalyAnomaly-based intrusion detection system Figure 3 from review on anomaly based network intrusion detectionWhat is an intrusion detection system?.

Anomaly-based intrusion detection system
Detection intrusion anomaly based system systemsAnomaly based intrusion detection system Detection intrusion anomalyComputer security and pgp: what is ids or intrusion detection system.
Passive deployment of network‐based intrusion detection systemAnomaly intrusion ids proposed Detection anomaly intrusionTraining phase of an anomaly detection system..
Building smart intrusion detection system with opencv & python
[pdf] a survey on anomaly and signature based intrusion detection什么是ids(intrusion detection system)入侵检测系统?都有哪些类型?nids、hids、基于特征、基于异常等 Anomaly detection technique for intrusion detection figure 2 depictsIntrusion detection ids system snort systems work does server types linux security computer intrusions install activities.
Sequence diagram of anomaly detection system.Anomaly detection Anomaly-based intrusion detection systemAnomaly based ids examples.
Anomaly analyzer system architecture and data flow diagram.
Figure 1 from review on anomaly based network intrusion detectionIntrusion & anomaly detection Anomaly intrusion.
.


Anomaly Detection Technique for Intrusion Detection Figure 2 depicts

Anomaly Detection System – ElfiSystems

Anomaly-based intrusion detection system | Semantic Scholar

2: Anomaly-based IDS | Download Scientific Diagram
Anomaly-based intrusion detection system

Training phase of an anomaly detection system. | Download Scientific

Anomaly analyzer system architecture and data flow diagram. | Download